Metodología Completa de Enumeración Web y VHOST Fuzzing — Laboratorio Final
En este laboratorio se te da solo una IP y debes:
-
Identificar directorios y archivos
-
Buscar VHOSTs / subdominios ocultos
-
Agregar los dominios descubiertos a
/etc/hosts -
Volver a fuzzear los nuevos dominios
-
Busca parámetros GET/POST
-
Fuzzear valores para obtener información/flags
A continuación tienes la metodología exacta para completar la evaluación.
#️⃣ Enumeración de VHOST
Añadimos el dominio principal:
sudo sh -c 'echo "IP academy.htb" >> /etc/hosts'
Realizamos el fuzzing de subdominios usando el Host header:
ffuf -w /opt/useful/seclists/Discovery/DNS/subdomains-top1million-5000.txt:FUZZ \
-u http://academy.htb:<PUERTO>/ \
-H 'Host: FUZZ.academy.htb'
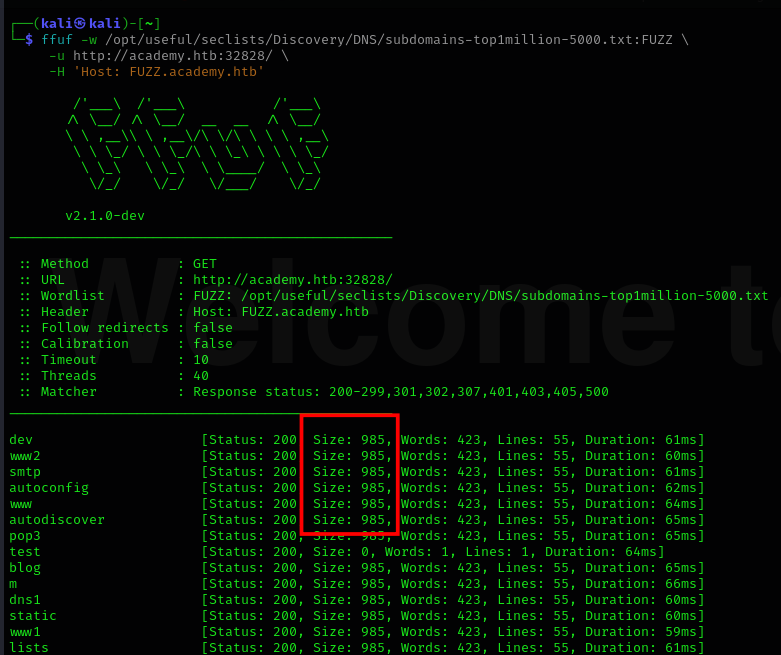
Filtrando tamaño: fs
ffuf -w /opt/useful/seclists/Discovery/DNS/subdomains-top1million-5000.txt:FUZZ \
-u http://academy.htb:<PUERTO>/ \
-H 'Host: FUZZ.academy.htb' \
-fs 985
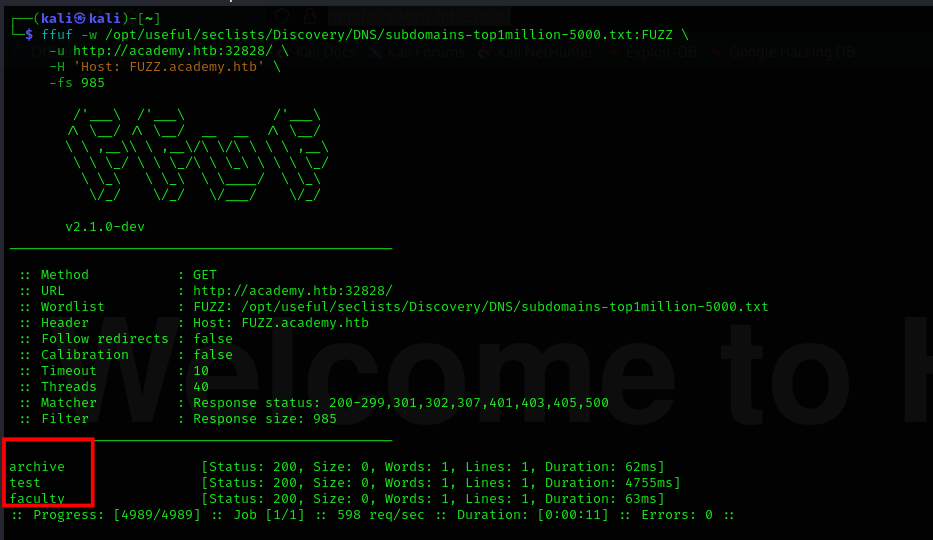
Subdominios encontrados:
archive,test,faculty
Añadirlos al hosts:
echo "IP archive.academy.htb" | sudo tee -a /etc/hosts
echo "IP test.academy.htb" | sudo tee -a /etc/hosts
echo "IP faculty.academy.htb" | sudo tee -a /etc/hosts
#️⃣ 1 — Fuzzing de Extensiones
ffuf -w /opt/useful/seclists/Discovery/Web-Content/web-extensions.txt:FUZZ \
-u http://faculty.academy.htb:<PUERTO>/indexFUZZ
ffuf -w /opt/useful/seclists/Discovery/Web-Content/web-extensions.txt:FUZZ \
-u http://test.academy.htb:<PUERTO>/indexFUZZ
ffuf -w /opt/useful/seclists/Discovery/Web-Content/web-extensions.txt:FUZZ \
-u http://archive.academy.htb:<PUERTO>/indexFUZZ
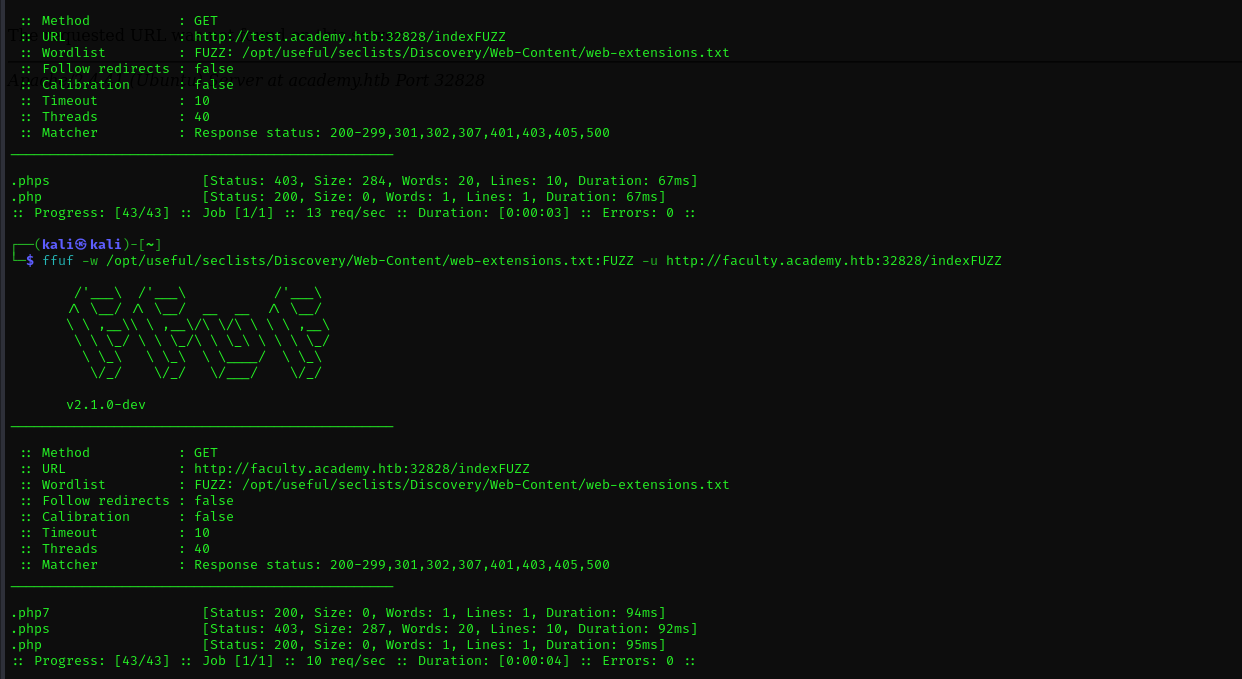
Extensiones válidas:
.php,.phps,.php7
#️⃣ 2 — Página que devuelve "¡No tienes acceso!"
Fuzz recursivo:
ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-small.txt:FUZZ \
-u http://faculty.academy.htb:49515/FUZZ \
-recursion \
-recursion-depth 1 \
-e .php,.php7,.phps \
-fs 0 \
-mc 200,301,302 \
-v
ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-small.txt:FUZZ \
-u http://test.academy.htb:49515/FUZZ \
-recursion \
-recursion-depth 1 \
-e .php,.php7,.phps \
-fs 0 \
-mc 200,301,302 \
-v
ffuf -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-small.txt:FUZZ \
-u http://archive.academy.htb:49515/FUZZ \
-recursion \
-recursion-depth 1 \
-e .php,.php7,.phps \
-fs 0 \
-mc 200,301,302 \
-v
La página restringida encontrada:
http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7
#️⃣ 3 — Descubrir Parámetros GET/POST
Obtener tamaño base:
curl -s "http://faculty.academy.htb:49515/courses/linux-security.php7" | wc -c
Resultado: 774 bytes
🎯 GET fuzzing
ffuf -w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt:FUZZ \
-u "http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7?FUZZ=test" \
-fs 774
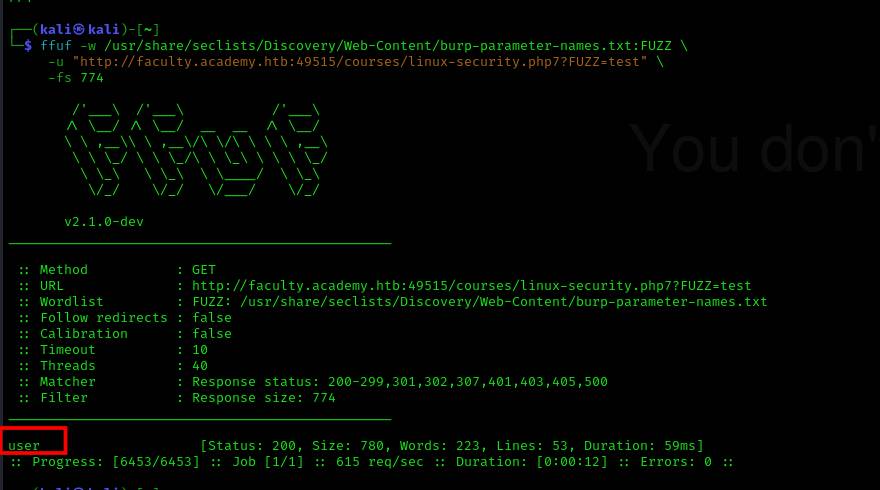
Parámetro encontrado:
user
🎯 POST fuzzing
ffuf -w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt:FUZZ2 \
-u "http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7" \
-X POST \
-d "user=test&FUZZ2=value" \
-H "Content-Type: application/x-www-form-urlencoded" \
-fs 774
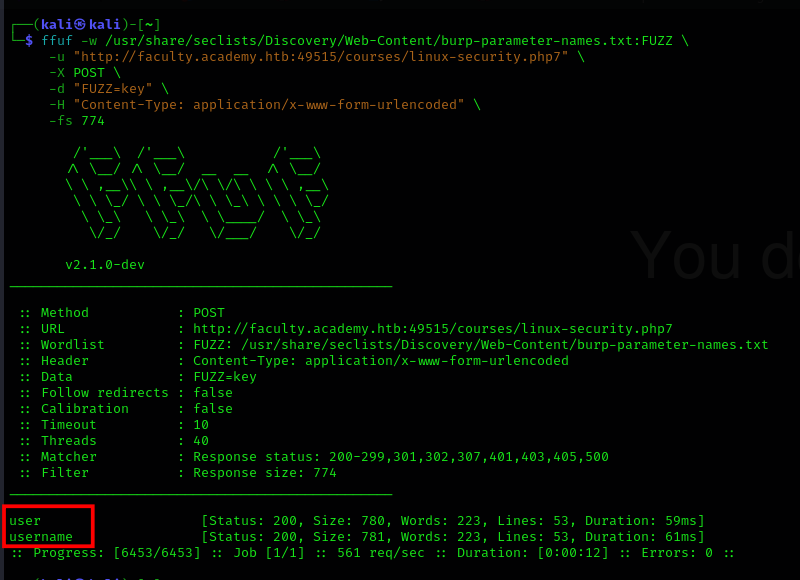
Parámetros válidos:
user,username
#️⃣ 4 — Fuzzing de valores (descubrir usuario válido)
Wordlist usada:
xato-net-10-million-usernames.txt
Verificar cambio de tamaño:
ffuf -w /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt:FUZZ \
-u "http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7" \
-X POST \
-d "user=FUZZ" \
-H "Content-Type: application/x-www-form-urlencoded"
Buscar valor válido:
ffuf -w /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt:FUZZ \
-u "http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7" \
-X POST \
-d "username=FUZZ" \
-H "Content-Type: application/x-www-form-urlencoded" \
-fs 780
Usuario encontrado harry

Comprobación:
curl http://faculty.academy.htb:<PUERTO>/courses/linux-security.php7 \
-X POST \
-d 'username=harry' \
-H 'Content-Type: application/x-www-form-urlencoded'